Latest Analyst Report: The 2023 Gartner® Market Guide for Supplier Risk Management Solutions
Prevalent Third-Party Risk Management Platform Version 3.14 Unifies Vendor Risk Monitoring and Assessment
I am very excited to announce that the 3.14 release of our Third-Party Risk Management (TPRM) Platform is available today! This release represents a significant milestone as it features integration between the platform and our cyber and business monitoring solution, VTM, delivering promised integration on time and leapfrogging other providers in this space to deliver you a complete 360-degree view of your vendor risks.
Here is what you can expect in this significant release…
Integrated Native Threat Monitoring
Utilizing questionnaire-based assessments provides a deep internal view of vendor security policies, processes, and controls. But many organizations miss out on the value of the other half of the third party risk story – outside-in monitoring and reporting of vendor network cyber risks – as it typically requires multiple tools from multiple providers to analyze data for a single vendor. Unfortunately, this fragmented approach requires manual reconciliation to fully interpret risks. Without a single, integrated view of vendor risks, organizations suffer from gaps in coverage leading to an incomplete picture lacking context.
With the 3.14 release, the Prevalent Third-Party Risk Management Platform has delivered a single repository for assessing vendor security risks – inside-out and outside in – by integrating key data elements of the Prevalent Vendor Threat Monitor solution into the platform to create a Threat Card in the vendor profile. Key data elements included in the Vendor Threat Card include:
Data/Cyber risk attributes:
- Native vulnerability scanning with external cyber threat intelligence from online sensor networks, global threat databases, anti-virus users, and dozens of collaborating security partners
- Deep risk insights gleaned from more than 27 billion URLs, four billion IPs, 600 million domains, and all public IPv4 addresses – plus data on IP threats, phishing events, and data breaches.
Business risk attributes:
- A combination of technology, data analytics, and analyst insights to evaluate business risk
- Collect, categorize and score risk based on commercial due diligence, financial analysis, and cyber threat intelligence for operational, brand, regulatory/legal, and financial events.
For a representation of this new integration, please see the screenshot below.
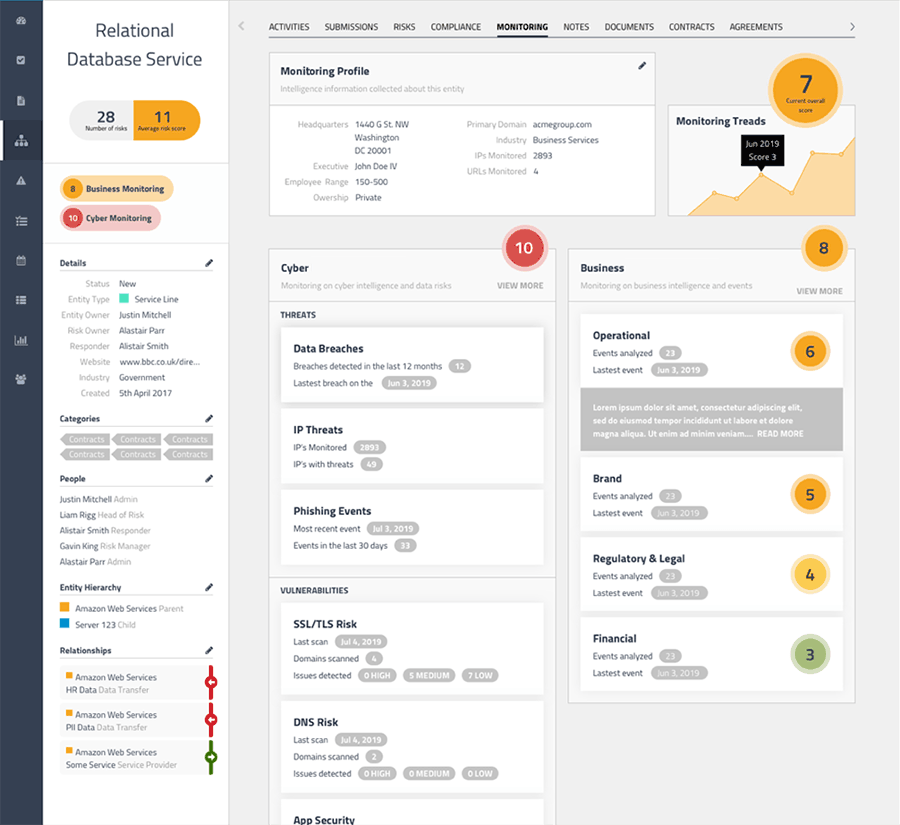
Why is this integration important? It enables you to centralize risk scoring, improve visibility and risk identification, accelerate remediation efforts, and periodically validate assessment data without leaving your preferred platform user interface.
In short, Prevalent has becoming the only true third-party risk management platform to deliver both inside-out assessments and outside-in monitoring in a single interface.
New RESTful API
All security and risk organizations utilize what can be a complex ecosystem of solutions to provide visibility into security risks. In fact, most companies have existing legacy systems aggregating data across dozens of areas. Naturally these teams must leverage existing technology investments to ensure their organizations are driving value from their risk reduction efforts. The problem is, though, some tools lack the capability to extract data automatically into other systems resulting in silos of risk data.
With version 3.14, Prevalent has addressed this challenge and created a RESTful API that enables over 65 unique attributes to be queried directly from the Prevalent platform so that customers can report on, query, manage, or assess platform data in other solutions.
For a representation of this new capability – including some of the attributes available through the API – please see the screenshots below.
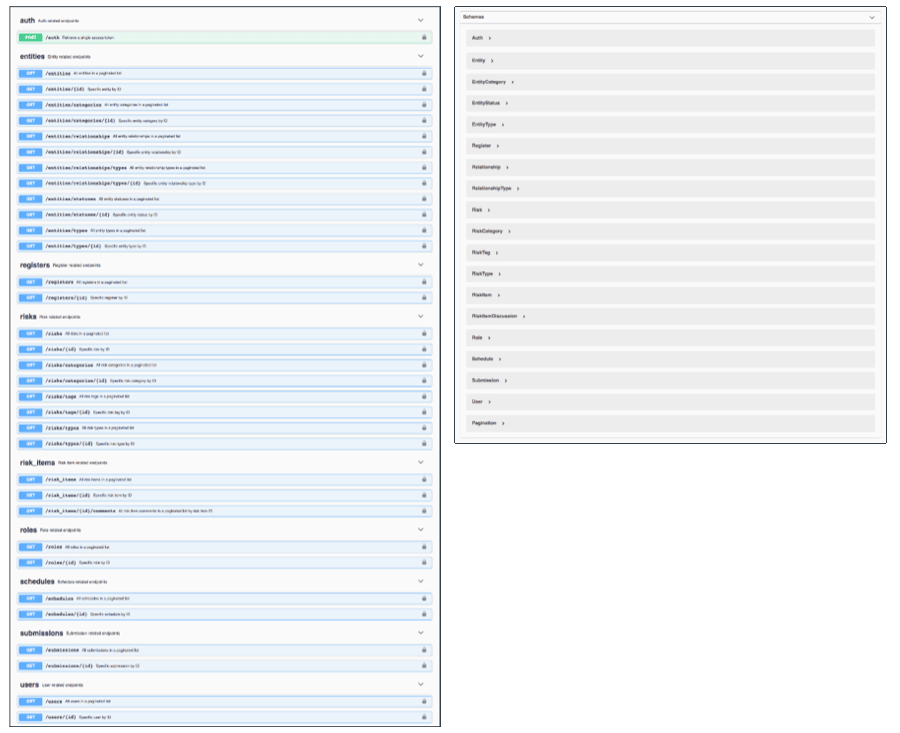
This enhancement provides customers with the ability to build their own connectors or leverage Prevalent’s connector capability to export data into other environments, helping to knock down silos and accelerate risk identification and remediation efforts.
For more on this significant release, please check out the What’s New document or view the brief new features demo. As well, be sure to read the release notes.
I think you would agree with me that this release represents a huge step forward for organizations wishing to improve their complete third-party risk management program.
-

Why Third-Party Monitoring Should Include Cyber and Business Risks
Business challenges, financial concerns, and reputational issues can often predict potential security risks. Learn how to...
04/11/2024
-

How Data-Driven Third-Party Risk Management Can Mitigate Ransomware Risks
This use case illustrates the value of combined internal controls assessment data and external third-party risk...
04/08/2024
-

The Third-Party Vendor Risk Management Lifecycle: The Definitive Guide
Your organization encounters distinct risks at each step of the vendor relationship, making it important to...
03/07/2024
-
Ready for a demo?
- Schedule a free personalized solution demonstration to see if Prevalent is a fit for you.
- Request a Demo




