RFx Management: How to Factor Risk into Sourcing & Selection

Requests for proposal (RFPs) and requests for information (RFIs) are essential for selecting the right products or services for your needs – and for choosing the vendors and suppliers who stand behind them. By automating your organization’s sourcing processes and infusing them with risk management best practices, you can increase procurement efficiency while reducing risk from Day 1 of the third-party lifecycle.
While many people are familiar with the terms RFP management and RFI management, there are several other request types that are used during the procurement process. This blog uses "RFx management" to encapsulate the various request types, which we will cover below.
This post explores key considerations for RFx management including:
- Defining RFx management
- Understanding potential RFx management challenges
- Classifying RFPs, RFIs and other types of requests
- Following the 5-step RFx process
- Using your RFx process to reduce third-party risk
What Is RFx Management?
RFx management is process of administering the identification, sourcing and selection of vendors, suppliers or other third parties. An effective RFx process should make it easy to:
- identify potential third-party products and services
- grade and compare solutions based on consistent criteria
- deliver insights into vendor/supplier risk prior to purchasing
- address stakeholder needs across departments
Most organizations begin sourcing and selection by submitting a Request for Information (RFI) to multiple vendors or suppliers, followed by a Request for Proposal (RFP) to a selection of finalists. RFI and RFP responses provide buyers with an understanding of the market and enable them to compare solution capabilities between providers. This can be followed by RFQs, RFTs and other informational requests until a final decision is made.
RFx Management Challenges
Many organizations are required – by company policy or by law – to conduct fair and objective evaluations of vendor solutions. However, most procurement teams are stuck with manual, spreadsheet-based RFx approaches for handling everything from tracking requirements and communicating with stakeholders, to conducting vendor due diligence and evaluating potential solutions. This makes the sourcing and selection process overly time-consuming, complex and inconsistent. It also increases the likelihood that vendor security and business risks will be overlooked.
Selecting the right vendor is just as important as selecting the right solution, so it’s essential for procurement teams to have streamlined processes for evaluating both. It’s also critical to select options that match the organization’s risk tolerance. The problem is, there are few options that enable teams to efficiently accomplish both objectives.
RFx Management Executive Brief
Learn about different vendor evaluation request documents, steps and challenges in typical RFx processes, and best practices for improving RFx automation and vendor risk visibility.

RF What? Understanding Request Types
Organizations can use different request types depending on the stage of the buying cycle they are in or the status of the vendor or supplier relationship. The most common request types are:
Request for Information (RFI)
RFIs are typically used early in the buying process to gather information about the potential vendors, suppliers and other third parties that may be able to address an organization’s needs. Companies that issue RFIs are seeking to learn about a specific market and determine basic requirements.
Request for Proposal (RFP)
RFPs are issued to vendors selected from the RFI process, or they can be used instead of an RFI if vendors and requirements are already identified. RFPs include detailed questions, criteria, and specifications, enabling buyers to compare options and make a final selection based on fit for purpose and fit for use.
Request for Quotation (RFQ)
RFQs are distributed to final candidates and ask for supplier pricing on requested goods or services. Some organizations bypass RFIs and RFPs and use RFQs for repeatable, simpler purchases that are typically based on price. Other organizations skip the RFQ process altogether and rely on sales negotiations instead.
Request for Tender (RFT)
RFTs invite suppliers to submit a sealed bid. These types of requests typically apply to legally structured organizations or government agencies.
Request for Bid (RFB)
RFBs invite prospective suppliers to bid on a service but are not considered a binding agreement. RFBs are used when the purchaser and suppliers have existing master services agreements (MSAs) in place and detailed vendor evaluation is not required.
Although most procurement use cases are considered either RFIs or RFPs, for the purposes of this blog we use RFx, where the “x” can stand in for any of the terms above.
The Five-Step RFx Process
To ensure that vendor evaluations are consistent and fair, organizations typically follow a standard five-step process. Note that each stage of the process presents unique challenges that can potentially slow purchasing cycles and introduce unnecessary costs and risks.
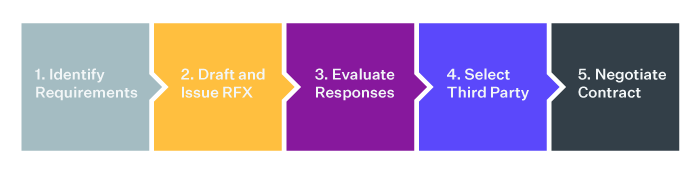
Step 1: Identify Business Requirements
At this step, procurement teams identify and determine the needs of internal stakeholders, as well as keep track of requirements as they evolve. Tasks can include scheduling and managing team meetings to develop and review requirements, in addition to investigating options available in the market.
With multiple people from several different internal teams involved in RFX processes, it can be challenging to bridge departmental silos and keep the project on track. Procurement teams must encourage collaboration while avoiding complexity – or buyers may attempt to circumvent the process altogether.
Step 2: Draft and Issue RFx
Here, procurement and business teams partner to draft questions to evaluate vendors based on the key criteria and outcomes defined in Step 1. They must also create the vendor data collection instrument, such as a spreadsheet, circulate it for review and approval, and define scoring thresholds. Finally, procurement or line-of-business teams communicate with candidate vendors about timelines, answer their questions, and clarify requirements. This step can involve a ton of back-and-forth email.
Step 3: Evaluate Responses
This step involves collecting and collating responses from multiple vendors, reviewing answers to determine fit, applying the scoring model developed in Step 2, populating comparison tables, and following-up with vendors for clarification if needed.
Organizations typically use spreadsheets to collect vendor information for comparison and evaluation, but spreadsheets can be time consuming to manage, too rigid for collaboration, and require teams to manually copy scoring formulas, resulting in an inconsistent, inaccurate or unfair evaluation. Procurement teams can’t afford to slow the business down.
Step 4: Select Third Party
At this step, the RFx leader convenes the team responsible for selecting the solution, confirms the winning vendor, and defines the next steps. This step also involves notifying the winner and communicating next steps.
Most RFx processes focus on selecting a solution with the right capabilities, but they often deliver little to no visibility into the risks that the vendor could introduce. Without understanding a potential vendor’s cybersecurity exposures, data breach history, regulatory concerns, financial issues, or reputational problems, organizations risk acquiring the right solution from the wrong vendor.
Step 5: Negotiate Contract
Once a vendor has been selected, and the solution is determined to be both fit for purpose and fit for use, procurement then notifies the legal team to begin the vendor contracting process. As with prior steps, this can involve manual email communications that don’t include an audit trail.
Using Your RFX Process to Reduce Third-Party Risk
Your organization's RFX process should enhance and improve upon your broader third-party risk management (TPRM) program. For instance, the sourcing and selection process is a great opportunity to grade a vendor’s profiled risk based on the criticality of their services and other factors. Here are a few best practices for integrating RFx with TPRM:
Require Audits & Accreditation for Certain Vendors
Vendor risk questionnaires should be used for all vendors that your organization works with. However, for RFIs and RFPs evaluating vendors that would have access to your systems and data, consider requesting evidence of security controls specified by industry guidelines such as NIST 800-53, NIST 800-161, the NIST Cybersecurity Framework, or ISO 27001.
Validate Vendor-Reported Controls When Possible
Some vendors may misreport information about their operations and security controls when responding to RFP requests. By integrating your RFx process with a third-party risk management (TPRM) platform, you can validate vendor-reported controls information against externally observable evidence about their business practices, finances, reputation, breach history, and cybersecurity exposures. Look for TPRM platforms that offer access to a vendor intelligence network and continuous risk monitoring capabilities to tap into these insights.
Don’t Go It Alone
Prevalent RFx Essentials is a SaaS solution that centralizes and automates the distribution, comparison, and management of requests for proposals (RFPs) and requests for information (RFIs). RFx Essentials makes it easy for your procurement team to not only select solutions and vendors that meet your organization’s functionality and risk requirements, but also take a critical first step in managing risk throughout the third-party lifecycle with built-in vendor risk intelligence. With Prevalent RFx Essentials organizations can:
- Speed purchasing cycles by automating and centralizing time-consuming internal and vendor communications
- Unify internal teams with a single, centralized platform for requirements management, communications and selection
- Make better risk-based decisions with comprehensive vendor business, reputational and financial intelligence
- Reduce human error and bias by automating manual tasks and enabling direct comparisons
- Validate what the supplier has provided in their RFP response with external intelligence
- Gain better risk visibility earlier in the relationship for faster, more targeted risk assessments later in the lifecycle
- Accelerate auditing and reporting with centralized documentation and supporting evidence
- Simplify contracting processes by automatically moving vendors into the contract lifecycle and pre-contract due diligence upon selection
RFx Essentials provides automation and intelligence for the first step in the third-party lifecycle, and natively integrates with the Prevalent Third-Party Risk Management Platform. For more on how Prevalent can help, request a demonstration today.
-

Vendor Offboarding: A Checklist for Reducing Risk and Simplifying the...
Follow these 7 steps for more secure and efficient offboarding when third-party relationships are terminated.
10/17/2024
-

Supplier Risk Management: The Definitive Guide
Supplier Risk Management (SRM) is increasingly raised as a board-level topic as business continuity concerns and...
08/01/2024
-

Supplier Compliance: Key Regulations to Consider for Your SRM Program
Organizations are increasingly being held accountable for compliance in their supply chains. Be sure to review...
07/25/2024
-
Ready for a demo?
- Schedule a free personalized solution demonstration to see if Prevalent is a fit for you.
- Request a Demo




