2021 Third-Party Risk Management Study: What Lurks Beneath the Cyber Risk Surface?

If your third-party risk management (TPRM) program is focused solely on cybersecurity, then you’re only getting a partial view of risk – what’s commonly visible above the water line. But so much more risk exists below the surface. For example, do you know whether your vendors are meeting SLA requirements? Can you assess the strength of their ethics and anti-bribery and corruption (ABAC) policies? How socially and environmentally conscious are your supplier chain partners?
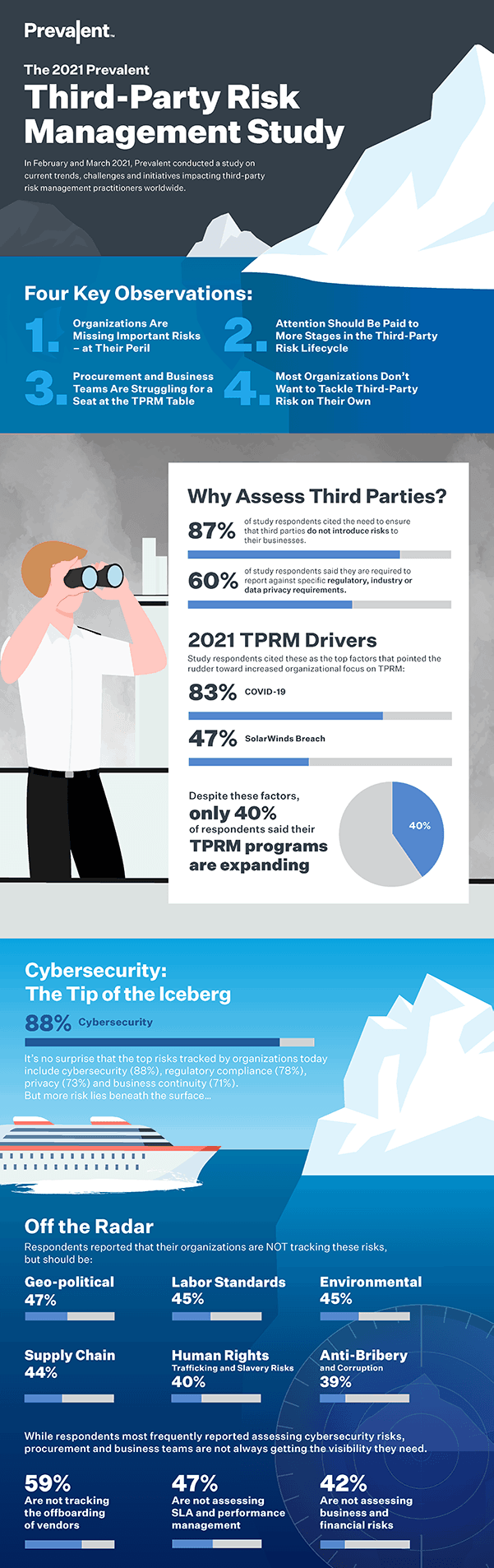
Prevalent recently surveyed senior decision makers about their organizations’ TPRM focus areas, stakeholders and challenges. Our goal was to understand the current, real-world state of third-party risk management programs. What we found is that many companies struggle to identify the reputation-wrecking business risks that lurk beneath the cybersecurity surface.
In the Prevalent 2021 Third-Party Risk Management Study, we present the full results of the survey and chart strategies for navigating the icy waters of vendor and supplier risk today. This post shares key findings from the study and outlines guidance for expanding your risk visibility throughout the third-party lifecycle.
Key Findings from the 2021 Third-Party Risk Management Study
Results of this year’s study point to four primary observations:
Organizations Are Missing Important Risks – at Their Peril
Two of the biggest events of 2020 – the COVID-19 pandemic and the social and racial justice movements – had little to do with cybersecurity but triggered important third-party risk activities. In fact, 83% of study respondents reported that the pandemic spurred an increased focus on third-party risk at their organizations. However, while the pandemic brought unprecedented challenges for supply chain risk management and vendor performance management, fewer than half of respondents were actively tracking supply chain and performance risks.
At the same time, the ongoing justice movements underscore the importance of working with partners who have sound diversity and ESG policies. Despite this, the study found that few companies actively track third-party risks related to labor standards, the environment and human rights.
Attention Should Be Paid to More Stages in the Third-Party Risk Lifecycle
Every third-party business relationship follows a lifecycle along these lines: pre-contract due diligence, contracting, onboarding, risk assessment, performance management, and offboarding. Interestingly, the number-one challenge cited by study respondents was a lack of pre-contract due diligence. More surprisingly, 59% of companies say they do not actively assess third-party risks during offboarding, which can open the door to data exposures and compliance violations. Need further proof? Just ask Morgan Stanley.
Procurement and Business Teams Are Struggling for a Seat at the TPRM Table
Third-party risk management has long been the domain of IT and security teams. Our study affirms this, with 50% of respondents reporting that IT and security own TPRM in their organizations. And 55% of organizations saw increased ownership by security over the past year. The problem is, only 22% saw an increase in ownership by procurement teams. This trend is concerning, as risks increasingly fall outside of the typical cybersecurity area of responsibility.
Most Organizations Don’t Want to Tackle Third-Party Risk on Their Own
70% of respondents indicated that outsourcing is the preferred method of managing third-party risk. Why? Because a shockingly large number of practitioners (42%) still use spreadsheets as the primary mechanism for vendor risk assessments – and 65% aren’t satisfied with this approach. Respondents also cited the need for a broader range of third-party risk intelligence sources a key to achieving TPRM success.
Click the preview to download a PDF of the complete infographic.
Recommendations for Keeping Your Third-Party Risk Management Program Above Water
Here are four (4) recommendations to chart a better course through third-party risks:
#1 – Expand Assessments Beyond Cybersecurity
Vendor risk management isn’t just a security and compliance problem. Many types of risks can impact an organization’s ability to produce, manage, and distribute goods and services. Therefore, security and business teams must work together to expand the scope of vendor risk assessments to include two areas in addition to cybersecurity:
- Reputational intelligence on legal actions and sanctions, executive leadership changes, politically exposed persons (PEPs), adverse media, state-owned enterprises, OFAC violations, and other indicators of potential cybersecurity or compliance problems.
- Financial information including performance, turnover, profit and loss, shareholder funds, and other indicators.
Look for solutions that normalize monitoring data and correlate it against risk assessment findings to escalate potential risks and identify recommended remediations. Incorporating a broad range of risk intelligence sources will help security and procurement teams make better-informed decisions.
#2 – Bridge the Gap Between Business and IT
Disjointed approaches to assessing third-party risk leave gaps – and gaps introduce risk. You can unify IT security and business teams with a TPRM platform solution that provides a central source for everything from vendor profiles and contracts, to assessment results and compliance reports, to performance metrics and remediation logs. Having a single solution ensures that the entire organization is using the same data to make risk-based decisions.
#3 – Manage Risk at Every Step of the Third-Party Lifecycle
Security, compliance and operational issues can crop up at any time during a vendor or supplier relationship, so it’s important to address risk at each stage of the third-party lifecycle. Be sure to download the full report for guidance on what look for at each step of the vendor risk lifecycle, including:
- Sourcing and Selection
- Intake and Onboarding
- Inherent Risk Scoring
- Vendor Risk Assessments
- Continuous Risk Monitoring
- SLA and Performance Management
- Offboarding and Termination
#4 – Outsource the Hard Stuff
The results of this study show that the preferred method of TPRM includes outsourcing on some level. Third-party risk management experts can manage the vendor lifecycle on your behalf – from onboarding vendors and collecting evidence, to reviewing assessments for completeness, identifying risks, and providing remediation guidance. As a result, you can safely navigate dangerous waters by efficiently scaling your TPRM program, reducing vendor risk, and simplifying compliance without burdening your internal staff.
The 2021 Third-Party Risk Management Study
This definitive report from Prevalent is loaded with insightful data, analysis and recommendations from our survey of global risk management practitioners.

How Do You Navigate Third-Party Risk?
We found that most companies are missing key risks at more than one stage of the vendor risk lifecycle, leaving their companies exposed to unseen risks. How is your third-party risk management program navigating these challenges compared to the respondents to our survey? Download the full results and review the infographic to benchmark your own TPRM practices.
For more on how Prevalent can help address third-party risk management challenges, request a demo of our platform today.
-

61% of Companies Have Been Breached by a Third Party...
Read the findings from our annual TPRM study and implement these best practices to put out...
05/08/2024
-

2023 Gartner® Market Guide for Supplier Risk Management Solutions Cites...
Prevalent believes it is differentiated by delivering comprehensive coverage of multiple risk types and by delivering...
12/12/2023
-

Prevalent Named a Leader in the 2023 SPARK Matrix™ for...
Leading industry analyst firm recognizes Prevalent for sophisticated Vendor Risk Management offerings.
11/06/2023
-
Ready for a demo?
- Schedule a free personalized solution demonstration to see if Prevalent is a fit for you.
- Request a Demo




